One Thing To Do Today: Tuesday Sweep, where are your backups?
TL:DR Sign up for Crashplan with the option of managing your own keys.
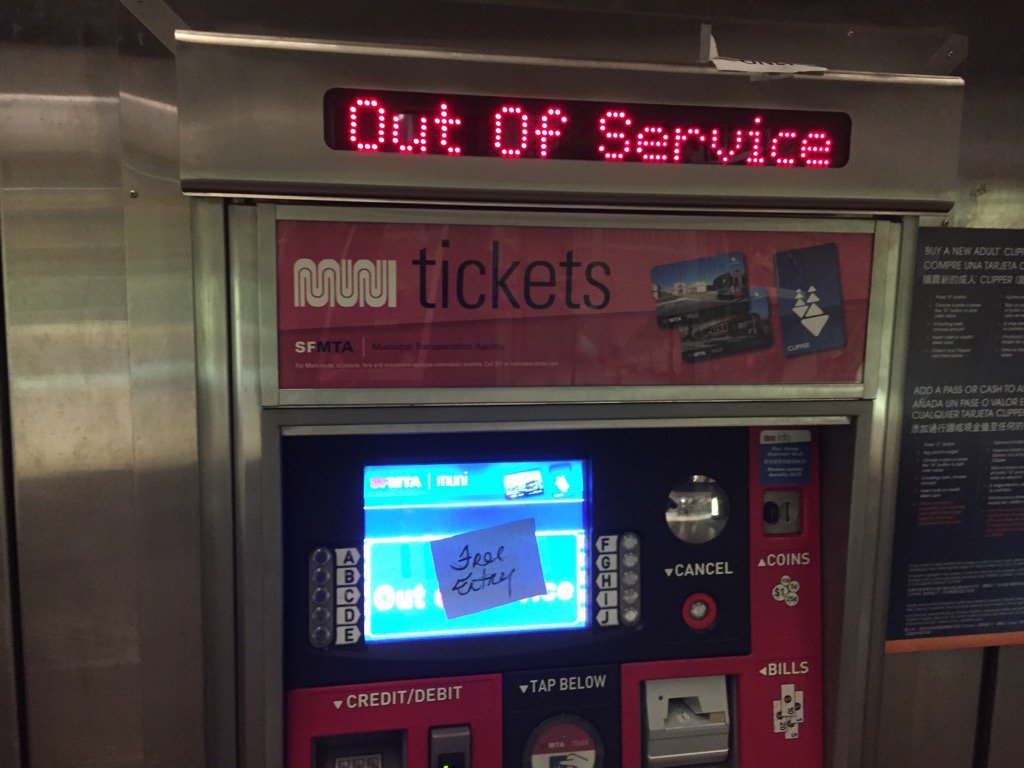
The SFMUNI was able to tell the folks who ransomed their system to go to hell. Why? Back-ups. There’s no reason not to wipe it all and start fresh if there is a back up. How liberating. Any backup plan has levels, multiple copies, etc. Ideally as automated as possible. Making sure all backup systems are up and running should be part of the Tuesday Sweep (link a work in progress). Keep strategies upto date to fight increasingly sophisticated ransomeware. Here are some of the items on my list to keep tabs on.
Password Manager Data
Backup the data file for your password manager. On a disk, to the cloud, somewhere. One of the criteria for selecting a password manager should be the ability to create secure backups. Check to make sure everything is synced up.
Active Files
GitHub, Dropbox, iCloud, Google Drive. Most of my work doesn’t require delicate handling. It’s probably headed towards being open source anyway. If I’m making a lot of changes on a file, my active copy gets synced regularly via one of these services. I’m making the conscious choice that losing the data would be more traumatizing than it getting out into the world.
It is possible to set up your own server to mimic some of these services, but I don’t want to maintain one. I’m also not sure that random hosting companies have the same war chest to stand up for my privacy as Apple has been willing to do. So my choice for handling data that requires more care would not be to roll my own cloud service, but to encrypt the files before either uploading or putting the files on a usb drive. (Although, not a USB drive I didn’t buy myself.)
Local boot drive
If all the urgent files live in the cloud, having a boot drive with just the operating system and some diagnostic tools might be enough to get back to productive under deadline. It won’t need to be updated all that often because it only has the basics.
Mac Advanced | Ubuntu directions for Windows | Official Windows Directions | Non-Official Windows Instructable (untested, but intriguing)
Searching Stack Exchange for the operating system you’re making the boot drive for with the name of the operating system you’re making the boot drive with, if different, will locate resources for your particular situation. Doing daily computing off boot drive is a topic for another day.
Full Local / Cloud backup
So this was going to be two separate sections, but the thing is, nobody really remembers to go to the trouble of manually backing up their computer to an external hard drive. Oh, and then to take the extra step of dropping it off at a safety deposit box or other offsite location? If your threat level feels that immanent you’ll have the motivation, but there are worthwhile steps to take that are less extreme.
The ideal setup is a software/service that will let you do both onsite and offsite one sweep. The Wire Cutter’s extensive review recommends Crashplan. I might switch. The free version allows you to backup locally, so if you want to do the sneaker-net offsite plan I poo-pooed above, you can do it. Getting two drives and alternating which one gets used will help prevent viruses of any type from reaching your data. The one-computer cloud backup plan is inline with others in the market at about $60/year. For $150/yr up to 10 computers can come under their care. They even have plans for small businesses.
The dealbreaker for a cloud storage should be the ability to manage your own encryption keys. Most will recommend against it because they don’t want someone willy-nilly choosing to do that without understand the gravity of the choice. If you manage your own keys, losing them means complete loss of data. There will be nothing they can do to help. That’s the right answer. However, if the threat of data loss makes you hesitate, please don’t. There is a perfectly valid half measure of letting them manage the keys for the main backup, but keeping personal information encrypted locally.
Having backups to revert to is protection against all sorts of malware and ransomeware attacks. No security will be full proof, so knowing what to do when the bad inevitably happens can make security preparations more relaxing. If this is all too much to put in place today, I nominate making sure that the password manager datafile has a secure second location and then signing up for Crashplan. Baby steps. Next time you’ll do more.
Image Credit: Lisa Amin Gulezian
@LisaAminABC7, https://twitter.com/LisaAminABC7/status/802693810983579648/photo/1 via Mashable