Tuesday Sweep: Jan 10 2016
Another week, another sweep. Even when other posts die down after the 20th, this post will still be here. Let me know what you’d like to see.
Reflect
What’s are the frictions keeping you from doing “what’s right”? Regret is only useful if it leads to a plan on how to improve.
My confessional: Sometimes if all the plugins I have enabled on my browser keep me from seeing a site I feel has information relevant to one of these pieces, I hop over to a second browser and load it there. That approach works partially because I have to choose actively to make that choice, reducing lazy loading. Yet, while incognito mode will generally zot most local files, it doesn’t really prevent tracking. By letting a webpage load all its javascript from the same computer, on the same network, as I do everything else, well, let’s just say that’s less than 1337 behavior. Possible remediation:
- Lock down that second browser even just a wee bit more.
- I never really took to that tablet we have. Could I set up us my sacrificial insecure browsing device?
- I could also look into researching these posts at my local public library, which provides computers. That would have the added advantage of encouraging me to engage with a local resource and perhaps help improve it for everyone.
Continuing Set Up
We’ve covered so much so fast. You’re not behind, you’re just where you are. Pick something to do.
- If you’re having trouble with all the set up, the coach tool at the Crash Override Network has a great step by step break down for many of the same introductory steps we did here.
- Review the list of OneThing articles so far and pick one to catch up on.
Sweep
This list will be getting longer, but lets keep it simple while folks are still setting up.
- Updated software recently? Pick a new device to check on today.
- Backups still up and running?
- Reduce your attack surface: Delete a low quality app from your phone. Delete an account.
- Double check privacy settings on your phone, social media accounts.
Learn
Where do you scan for news? I keep an eye out for recent exploits and breaches that have come to light, new tools, interesting idea’s, etc.
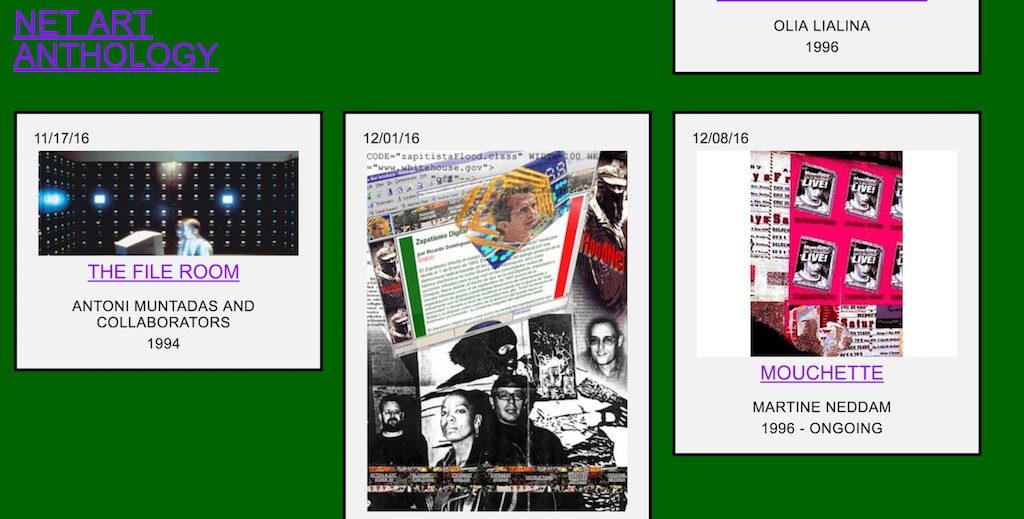
- Relevant Art: Rhizome is putting on a 2 year online exhibition called Net Art Anthology which will “present 100 artworks from net art history, restaging and contextualizing one project each week.” See the art that grew up with the hacker culture hand in hand.
- Course: Cory Doctorow is running a free Introduction to Cyber Security class at Future Learn.
- Podcast: For general audiences, The Code Breaker Podcast is a fun one.
- Many security sites aren’t done with their summaries for 2016 and outlooks for 2017
- From Ars Technica, article about exploits directed at the US intelligence accomplished via social engineering exclusively, and I guess advice to not buy D-Link products?
- Schneier writes about attributing hacks with special reference to how the DNC hacks were linked to Russia.
- For continuing training on how to think like a threat actor, Krebs’s Immutable Truths About Data Breaches.
- For Developers: Just Learned about the OWASP Top Ten Project – OWASP “A list of the 10 Most Critical Web Application Security Risks.” Handy list of things to avoid when designing software.
Engage
We are a community. You are a welcome part of it.