lsof in the wild
A zero day exploit on the video conferencing app Zoom for the Mac hit the news yesterday. The excellent write up by researcher Jonathan Leitschuh breaks down the multi-part problem.
- Zoom hosts control whether attendee’s camera is on by default
- The very first time you install Zoom on a Mac it spins up a local server that can forever and ever reinstall Zoom without any user interaction.
Leitschuh goes into why these represent vulnerabilities and what motivated Zoom to write their software for the Mac this way. This post is not about the Zoom exploit. This post was motivated by my dad, a man who has been fussing around with computers since the TRS-80, looking at the instructions for the fix and responding with essentially “I do what now?”
This may have been a ploy to get some father-daughter computer bonding time, but the full fix utilizes an amazing command available on unix based operating systems computer, lsof.
Written and maintained by Victor A. Abell, a HAM operator and retired professor from Purdue, the lsof utility provides a deceptively simple service. It retrieves a “list of open files.” Listing files wields awesome power on unix derived operating systems as everything is a file. Sockets, devices, text files, all communicate with streams of bytes and the file system catalogs them all. lsof plucks the desired streams from the morass of activity.
For example, in the Zoom article Leitschuh uses the following command to kick off the process of cleaning out that hidden server.
lsof -i :19421 While possible, running lsof with no modifiers spews thousands of records. The -i tells lsof to restrict what files it retrieves to internet and x.25 (HP-UX) network files, so lsof -i alone represents a powerful tool to find out who and what has been working with network protocols. The next argument sieves the results further. Adding :19421 tells lsof -i to look for any internet processes using port 19421, Zooms server port of choice Leitschuh discovered. Here are more examples using lsof -i
#using a port number, above, also good for 'port already in use'
lsof -i :[port]
#locate connections that are marked as listening or established
lsof -i -sTCP:LISTEN
lsof -i -sTCP:ESTABLISHED
lsof -i | grep -E 'LISTEN|ESTABLISHED'
#There are other ways to select by address:
#[46][proto][@host|addr][:svc_list|port_list]
lsof -i :https # all https connections
lsof -i @localhost # any connections to localhost
lsof -i @crashspace.org #... to crashspace
lsof -i 46 # IPv4 or IPv6 connections
lsof -i TCP # all TCP connectionsCombining lsof arguments hones the search. Want to find all the TCP or UDP connections from user dev4531 without trying to resolve the port numbers to port names for network files (for speed)?
lsof -u dev4531 -P -i TCP -i UDPThe same info but for everyone who is not dev4531?
lsof -u ^dev4531 -P -i TCP -i UDPThere are so many other useful examples that have nothing to do with network connections. Having trouble deleting a file because it’s in use?
lsof -t [file-name]
kill -9 [returned-pid]
lsof -t /Users/dev4531/Documents/whos_my_process.txt
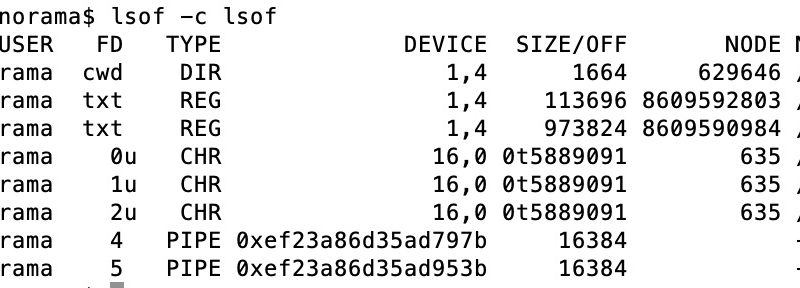
Need to see what files are being affected by an application you know the name of? More than one?
lsof -c [process-name]
lsof -c Google
lsof -c ssh
lsof -c ssh -c curl #returns ssh or curl filesGet a list of “open files” in a specific directory?
#Recursive
lsof +D [directory-path]
#Non-recursive
lsof +d [directory-path]
lsof +D /Users/dev4531/Documents/test_environment_dirThe results of lsof can be combined into other commands as well, for example if you want to kill all the processes of a specific user?
kill -9 `lsof -t -u [user]`
kill -9 `lsof -t -u dev4531`The list goes on and on and on as to what one can do, and tutorials providing a wealth of other examples:
- https://www.thegeekdiary.com/lsof-most-commonly-used-examples/
- https://danielmiessler.com/study/lsof/
- (covers repeat mode) https://www.thegeekstuff.com/2012/08/lsof-command-examples/
- extensive man page online https://linux.die.net/man/8/lsof
Spend some time shaking the file system with lsof and see what falls out.