One Thing To Do Today: Learn a new phrase “Threat Model”
Option 1: You know something can go wrong. “They” can get you …THEM…today it will be in some new way that sounds more William Gibson than real. You’re sure of it. Your tongue feels impractically large. Breakfast looks hostile. That’s okay though because there’s only a rock where your stomach’s supposed to be anyway. Defeated before a shower, you go back to bed while your IP security camera’s inner gaze quietly turns to its DDoS target of the day.
Option 2: Have a plan.
Threat Modeling. Security researchers call the cognitive behavioral therapy they use to stave off the crazy threat modeling. The threat modeling process forces generalized anxiety into a concrete shape so it can be killed.
The software development world’s version of threat modeling leaps into jargon fast. However, there are other templates we can use to get started. FEMA has a threat modeling process, for example. Defensive driving techniques represent a threat model mindset. All of these processes have a similar shape to them:
- What needs protecting?
- What are the “assets”
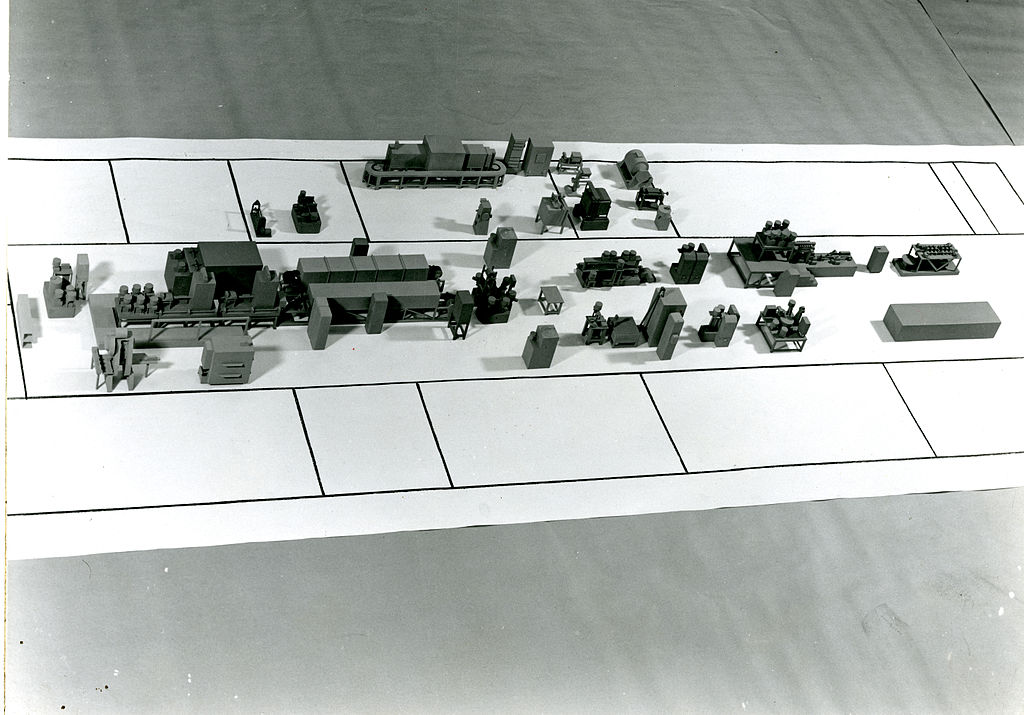
- Where do the assets spend their time? How do they travel? What are the detailed characteristic of that space? (Diagrams help.)
- What do they need protection from?
- Possible motivations / Addressable root causes
- Methods of attack: What direction and at what strength?
- How likely is this version of events?
- What can be done to make the asset safer?
- What’s fast and easy?
- Action plan for longer term projects.
- What happens when those protections fail?
- Fail safes
- Exit strategies
I raise the issue of threat models now since we’re getting towards the end of the super simple actions. A safe digital environment doesn’t come from bunch of bingey little actions, but from a changed mindset. There is a never ending list of what one CAN do so it’s necessary to have criteria for deciding what gets to the top of the list.
Different people pick different cornerstones to build their threat models on. Some start with the assets, figuring out what they care about first. Some start with the system, drawing a picture of what can be attacked. Others start from the point of view of the most threatening attacker, fortifying first what that threat actor would find the most juicy. Most end up as sort of a hybrid.
I’m most drawn to the first approach so I leave you with these questions. Set a timer for maybe 10/15 minutes and use them as a prompt for a free write. We’ll revisit them again.
- What gets carried out of your burning home? Burning office? Burning car?
- Could digital information be used to damage your sense of self?
- Imagine every item with a microphone, speaker, GPS, camera, any sensor at all in your environment are at a cocktail party. What funny stories about you are they telling?
- Picture a stranger going through your unlocked phone or computer. For the exercise they have any and all your passwords. Picture different types of information popping up on the screen. Vacation photos, banking info. What information could they be looking at when you walk in that would lead to the most embarrassment or anger? What about happiness? Are you even a little bit happy that something was discovered? What changes if instead of a stranger it’s a family member? A friend? A boss? A colleague? A corrupt law enforcement agent?
- Would that stranger/friend/boss be able to hurt people who aren’t you with what they find? Do you care? Maybe you don’t. That’d be good to admit.
Congratulations. NOW you can go back to bed.