One Thing To Do Today: Research Social-Engineering
TL;DR: Read the entire SmartFile article on 23 Social Engineering Attacks, or at the very least scroll to the end for their summary infographic.
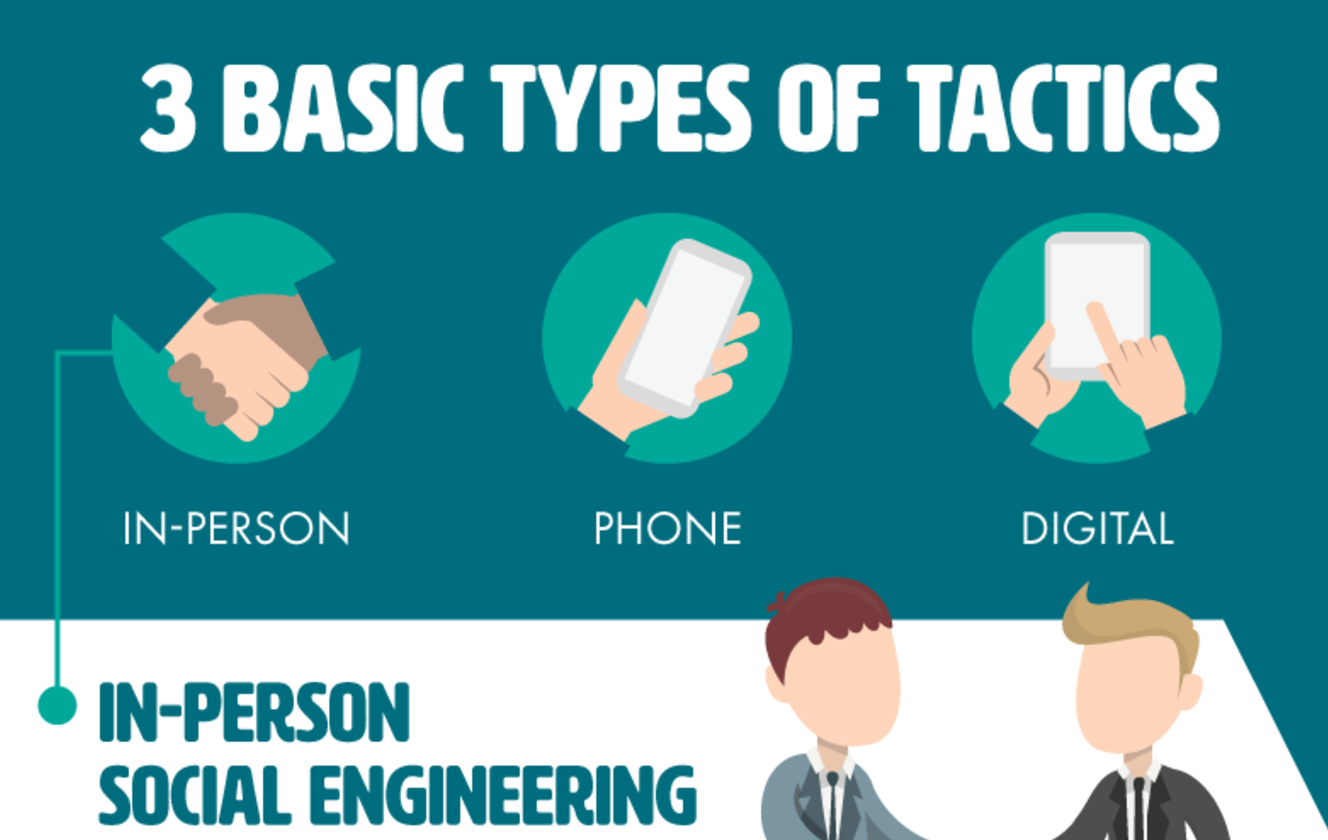
The very first thing I told people to do was download Signal. It was fast and easy for beginners. But if I may say so myself, it’s really kind of pathetic advice – “Here download this app, to your phone, which has location services enabled, and Facebook, and a microphone, which your unconscious thumbprint can unlock…” While 5-things click-baity guides have useful tips, there is a reason that the second and third steps I wrote about were techniques to get and hold our own attention. We ourselves represent the biggest vulnerability to any and all security efforts we attempt. Social engineering exploits convince people to give up their information, and feel good about doing it. A giant topic, all I can do is give a recommended reading/viewing list for non experts:
- SmartFile breaks down 23 social engineering attacks immediately followed by the way to stop them.
- Wth an excellent team Security through Education has an a page on how to protect yourself as well as a Podcast.
- In 2012 the Washington Post wrote a long article with lots of examples and names to know.
- How Con Artists Trick Your Mind via the BBC sums up a University of Cambridge paper (PDF) on seven security techniques.
- The HOPE conference has had a panel every year since 1994 on Social Engineering Search for “hope conference social engineering panel videos” (Duck Duck Go Search)
Some basic tips:
- Put something in your eye line to remind you be curious and listen to your spidey-sense
- Schedule a regular time to refine said spidey-sense
- “The clock is ticking” is a common ploy. Buy time for your spidey-sense time to work. Ask questions. Don’t try to act smart if you didn’t understand the answer. Follow up. Why do you need that? Why do we need to do it this way? What does that $JARGON_WORD mean? Who did you say you were with? Never agree to expose networks or information without enough time to check the story.
- Trust, but verify. If they say “so and so sent me,” for goodness sake check with “so and so.”
- Be wary of links, phone numbers and email addresses. Look up official channels directly.
- Keep in mind that typically trustworthy folks can be fooled themselves, get as close to primary sources as you can.
- Random downloads and external devices don’t belong anywhere near a secure machine.
To close on a personal note, I hate being the bearer of all this “don’t trust anyone or anything” news. It feels more negative about humanity than I actually am. The thing is, I’m a city girl. To expect someone to spend their time putting my best interests at the center of their day seems rude. Why should they? I don’t know what it takes to get through their night. The favor I can do my fellow humans is to not outsource my wellbeing to those who haven’t actively signed on to that deal. Humans survive as beautiful broken things. “Good people” participate in actual evil. “Bad people” have moments of grace. I try not to assume which I’m dealing with. Caution, curiosity and compassion don’t have to be at odds.